Where to put your server, in a private or public subnet?
Where should you put your server? If it is a web server probably in a public subnet. Wrong!
This article was originally posted on Medium
What a developer would do
Usually web developers run a server in a provider like Linode, they install the stack they need, and they deploy the code. This has serious implications regarding security: that server is exposed to the Internet and it is vulnerable. If you have a small budget and you have a small web app, probably it is the only way to go, although you should, at least, harden the server and set up the firewall (iptables if you are using Linux).
However, if you need HA, security, and scalability, you cannot just use one server. In this case, you will have at least a private and a public subnet. Even better, you should have a public subnet, a private subnet for your webservers and another private subnet for your DBMS, which would be a multi-tiered architecture. So which server goes where? You should put as many servers as you can in the private subnet unless you are really forced to put it in the public subnet.
A short list of rules to help you
Here is a short list of rules you should use when deciding where to put a server:
- Is the server needed to manage other servers? If yes, then it should go in the public subnet, because you will need to connect to that server first, via the Internet, then connect to the server you want to manage. A bastion server is a good example (OpenSHH server).
- Does the server provide a network service? If it is a load balancer, a NAT server, a Proxy, a VPN server, they should be in the public subnet, they all need access to the Internet, a direct access.
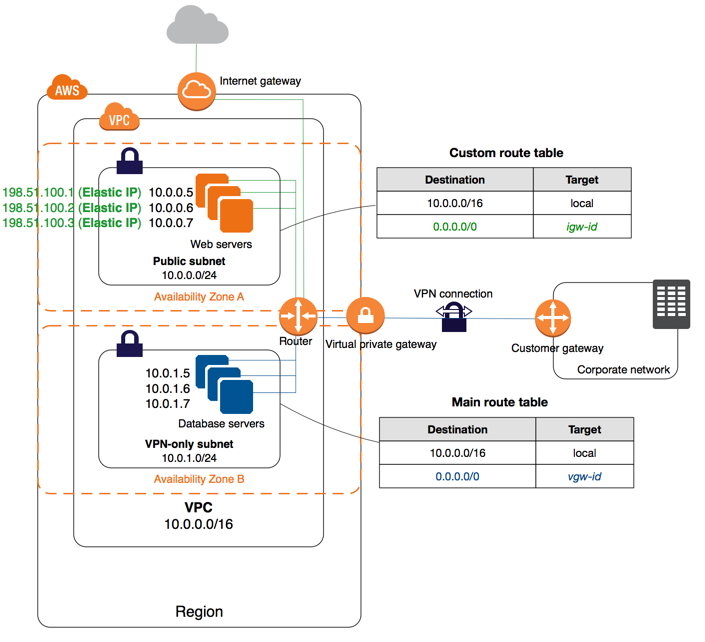
- Does the server need to replicate data in another DC? It should go in the private subnet and it should replicate via a VPN, a site-to-site connection. You want to send your data via an encrypted tunnel, and you want to make sure that only certain data will be allowed in your tunnel, by using AWS NACLs or a firewall.
- Does your server need to connect to external servers? If yes, you can put your server in the private subnet and route requests to the Internet (CIDR 0.0.0.0/0) to a NAT server, or NAT Gateway if you are using AWS.
- Do you have a load balancer which has to balance traffic coming from Internet and redirect the traffic to web servers in the public subnets? It should stay in the public subnet.
- Do you have a WAF, Web Application Firewall? Put it in the public subnet like the load balancer.
- Do you have a load balancer that is receiving traffic not from the Internet? It is an internal load balancer and it should stay in a private subnet.
An example
In the following diagram you can see how you could replicate the database state to a corporate network. Web servers are in the public subnet, but it would be netter to move then in the private subnet and receive web traffic via an ELB (Elastic Load Balancer).